Introduction
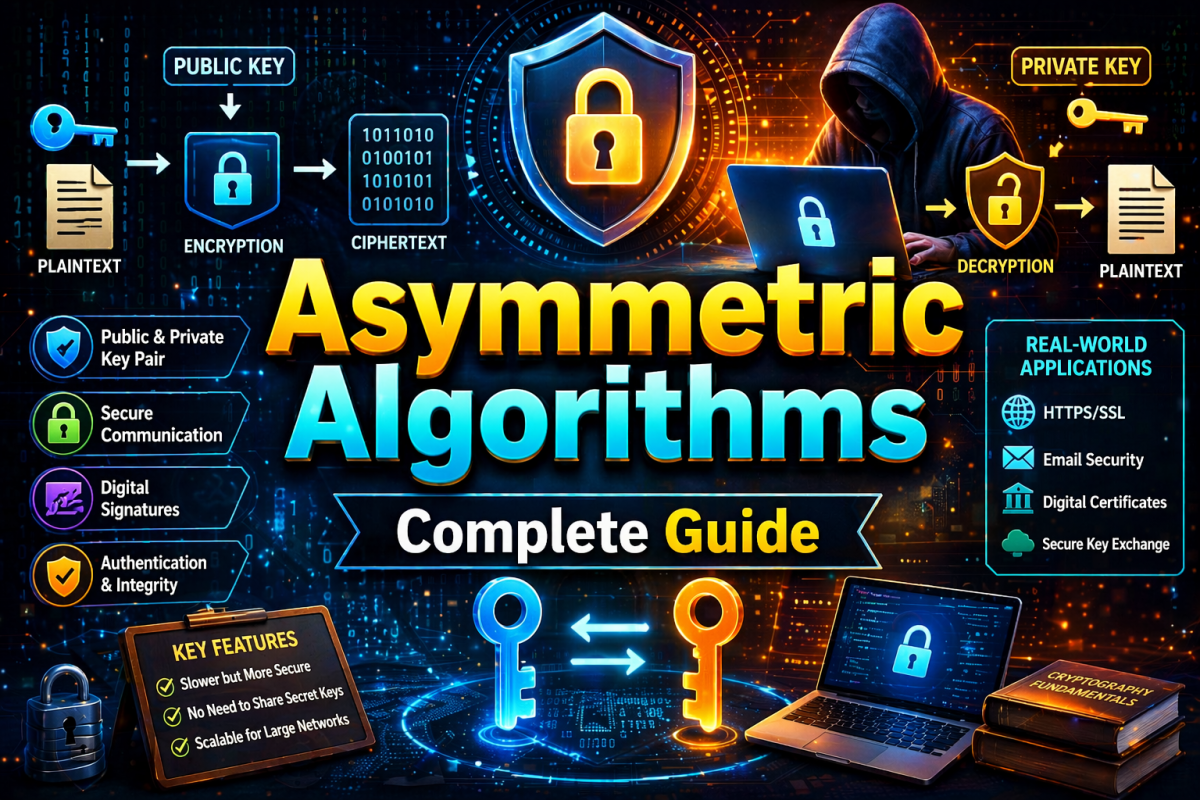
Asymmetric algorithms are one of the most important advancements in modern cryptography. They solve one of the biggest problems in symmetric encryption—secure key sharing. These algorithms are widely used in secure communication, digital signatures, and internet security.
1. What are Asymmetric Algorithms?
Definition:
Asymmetric algorithms are cryptographic techniques that use two different keys—a public key and a private key—for encryption and decryption.
Explanation:
Unlike symmetric algorithms, where the same key is used, asymmetric encryption separates the keys. The public key is shared openly, while the private key is kept secret. This makes communication more secure, especially over open networks like the internet.
Example:
If someone wants to send you a secure message:
They use your public key to encrypt it
You use your private key to decrypt it
2. Key Concepts in Asymmetric Cryptography
2.1 Public Key
Definition:
A public key is a key that can be shared openly with anyone.
Explanation:
It is used to encrypt data or verify digital signatures. Even though it is public, it cannot be used to decrypt sensitive data, which maintains security.
Example:
A website’s SSL certificate contains its public key.
2.2 Private Key
Definition:
A private key is a secret key kept only by the owner.
Explanation:
It is used to decrypt data encrypted with the public key or to create digital signatures. Protecting the private key is critical because its exposure compromises the entire system.
Example:
Stored securely in a user’s device or server.
2.3 Key Pair
Definition:
A key pair consists of a public key and a corresponding private key.
Explanation:
These keys are mathematically related. Data encrypted with one key can only be decrypted with the other. This relationship forms the foundation of asymmetric cryptography.
3. How Asymmetric Algorithms Work
Step-by-Step Process:
Receiver generates a key pair (public + private key)
Public key is shared with the sender
Sender encrypts message using public key
Encrypted message (ciphertext) is sent
Receiver uses private key to decrypt
Original plaintext is obtained
Explanation:
This process ensures secure communication without needing to share secret keys beforehand.
4. Encryption and Digital Signature Use
4.1 Encryption Use Case
Definition:
Using asymmetric algorithms to ensure confidentiality.
Explanation:
Data is encrypted with the receiver’s public key and decrypted with their private key. This ensures that only the intended receiver can read the message.
4.2 Digital Signature Use Case
Definition:
Using asymmetric algorithms to verify authenticity and integrity.
Explanation:
The sender signs a message using their private key. The receiver verifies it using the sender’s public key. This confirms that the message is genuine and not altered.
5. Characteristics of Asymmetric Algorithms
5.1 Two-Key System
Definition:
Uses a pair of keys instead of one.
Explanation:
This eliminates the need for secure key sharing, making it suitable for internet communication.
5.2 High Security
Definition:
Provides strong protection against unauthorized access.
Explanation:
Even if the public key is known, without the private key, decryption is practically impossible.
5.3 Slower Performance
Definition:
Asymmetric algorithms are slower than symmetric ones.
Explanation:
They involve complex mathematical operations, which require more computational resources.
5.4 Secure Key Distribution
Definition:
Solves the key distribution problem.
Explanation:
Public keys can be shared openly, removing the risk associated with sending secret keys.
6. Popular Asymmetric Algorithms
6.1 RSA (Rivest–Shamir–Adleman)
Definition:
A widely used asymmetric encryption algorithm.
Explanation:
It is based on the mathematical difficulty of factoring large prime numbers. RSA is commonly used in secure data transmission and digital certificates.
Example:
Used in HTTPS websites and email encryption.
6.2 ECC (Elliptic Curve Cryptography)
Definition:
An advanced asymmetric algorithm based on elliptic curves.
Explanation:
It provides strong security with smaller key sizes, making it efficient and faster compared to RSA.
Example:
Used in mobile devices and modern secure systems.
6.3 Diffie-Hellman Key Exchange
Definition:
A method for securely exchanging cryptographic keys.
Explanation:
It allows two parties to generate a shared secret over an insecure channel without directly transmitting the key.
Example:
Used in establishing secure connections in TLS.
7. Advantages of Asymmetric Algorithms
Secure communication over open networks
No need to share private keys
Enables digital signatures
Provides authentication and non-repudiation
Essential for internet security
8. Disadvantages of Asymmetric Algorithms
Slower compared to symmetric encryption
Requires more computational power
Not suitable for encrypting large data directly
Often used with symmetric encryption (hybrid systems)
9. Real-World Applications
HTTPS (secure websites)
Digital signatures and certificates
Secure email communication
Online banking systems
Blockchain and cryptocurrency
10. Asymmetric vs Symmetric (Quick Comparison)
| Feature | Asymmetric | Symmetric |
|---|---|---|
| Keys | Two keys | One key |
| Speed | Slow | Fast |
| Security | High | Depends on key secrecy |
| Use | Key exchange, authentication | Data encryption |
Conclusion
Asymmetric algorithms revolutionized cryptography by solving the key distribution problem. They are essential for secure communication in modern digital systems.
Although slower than symmetric algorithms, their ability to provide secure key exchange, authentication, and digital signatures makes them indispensable in cybersecurity.
Want to master Cryptography and Cybersecurity from basic to advanced?
👉 Join BNIT Computer Education
👉 Learn practical + theoretical concepts
👉 Industry-level training
👉 Build career-ready IT skills
Start today and become a cybersecurity professional.
BNIT Computer Education – Your Future in Technology Starts Here